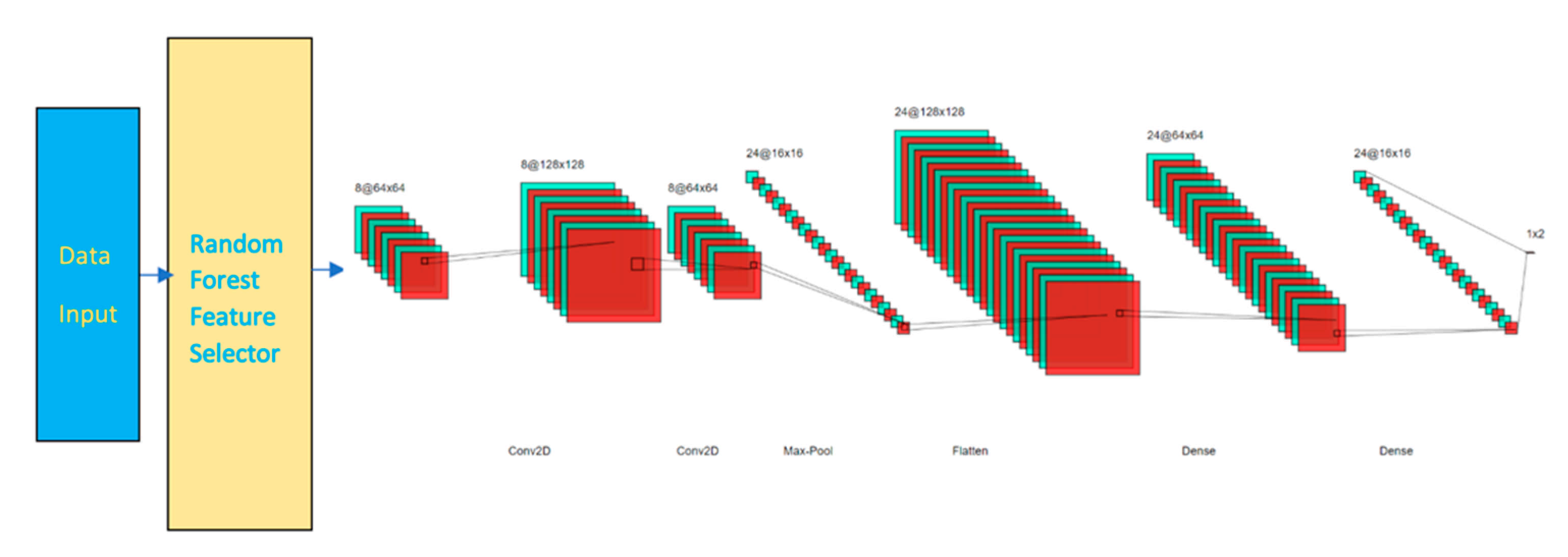
Sensors | Free Full-Text | Using Embedded Feature Selection and CNN for Classification on CCD-INID-V1—A New IoT Dataset

Numerical investigation of elliptical core few‐mode fiber for next generation data transmission - Mitu - International Journal of Communication Systems - Wiley Online Library

On the sliding-filament model of muscular contraction, IV. Calculation of force-velocity curves. | PNAS

Applied Sciences | Free Full-Text | AAAA: SSO and MFA Implementation in Multi-Cloud to Mitigate Rising Threats and Concerns Related to User Metadata

Energy Transfer‐Assisted Whispering Gallery Mode Lasing in Conjugated Polymer/Europium Hybrid Microsphere Resonators - Ngara - 2019 - Chemistry – An Asian Journal - Wiley Online Library

Feasibility of ultrasound tomography–guided localized mild hyperthermia using a ring transducer: Ex vivo and in silico studies - Pattyn - - Medical Physics - Wiley Online Library
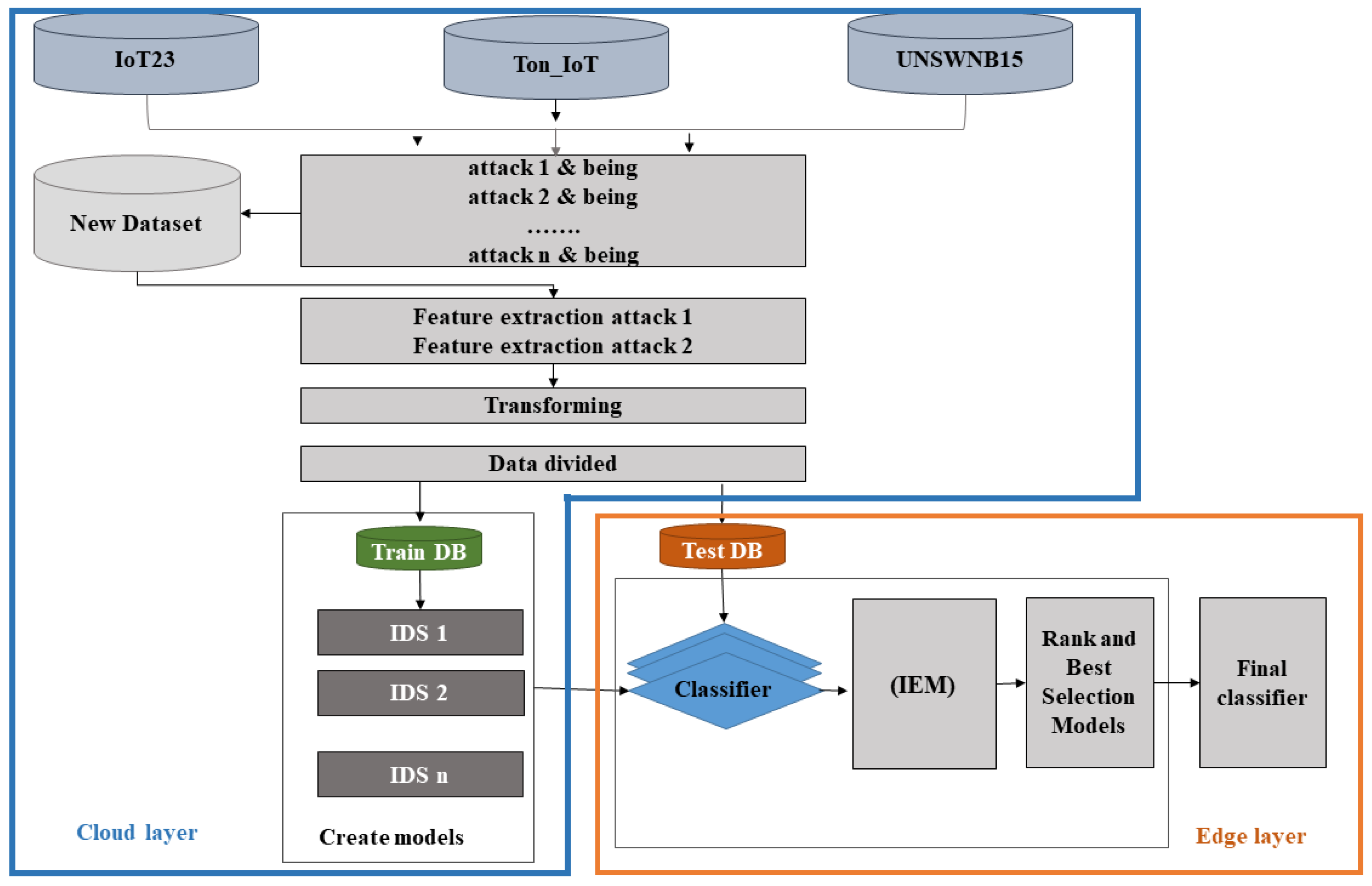
IoT | Free Full-Text | Evaluation and Selection Models for Ensemble Intrusion Detection Systems in IoT

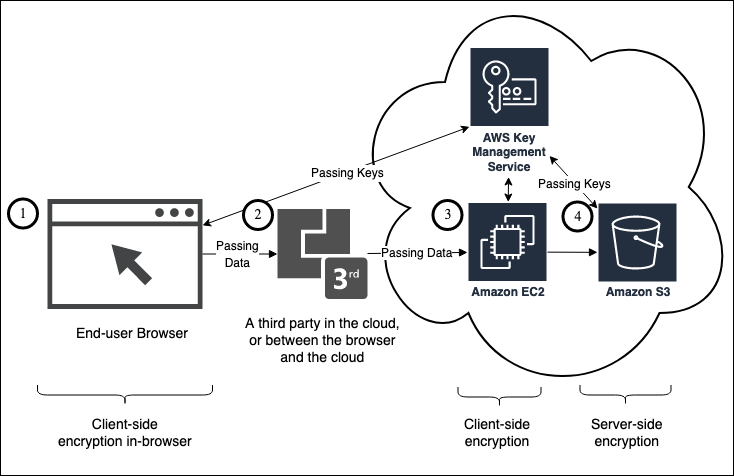
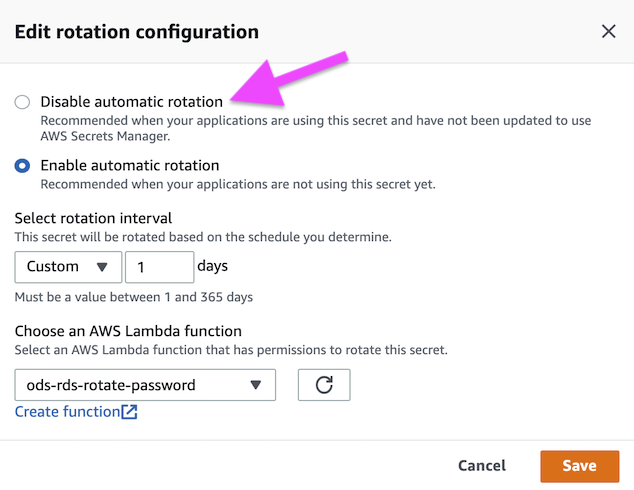
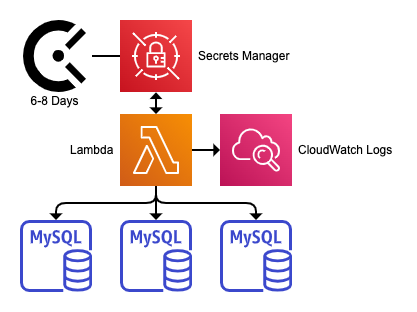
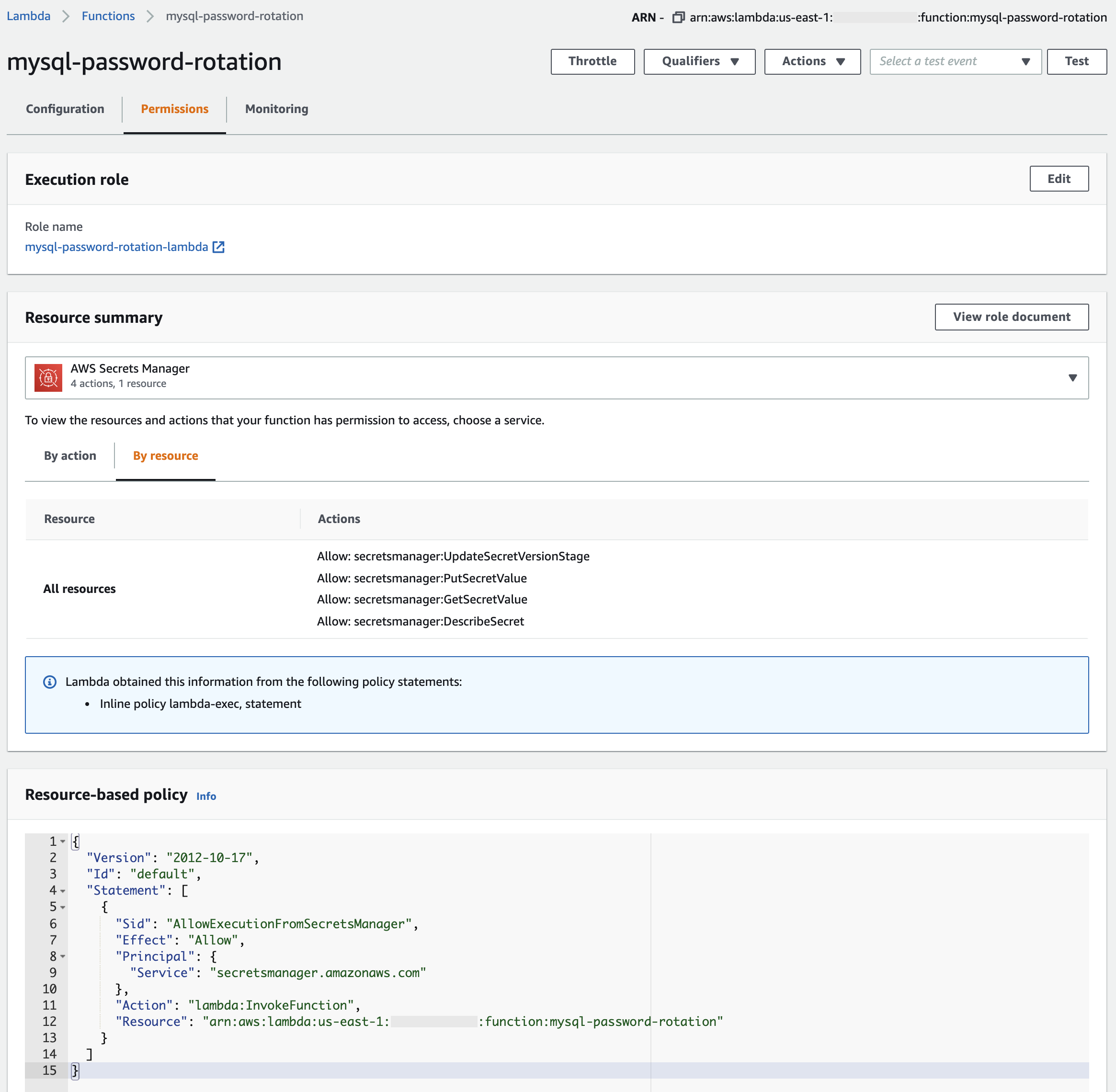
How to securely provide database credentials to Lambda functions by using AWS Secrets Manager | AWS Security Blog
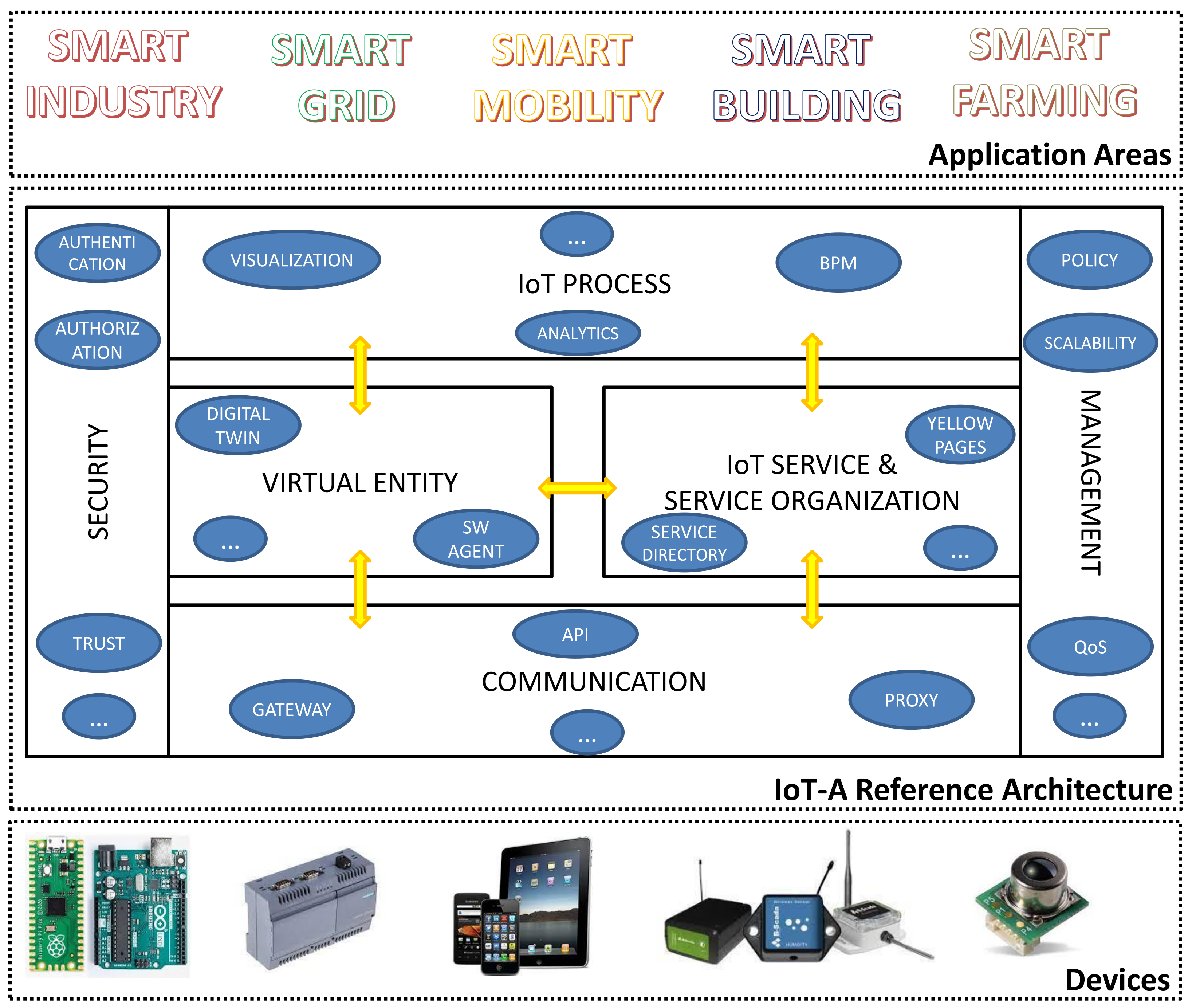
Sensors | Free Full-Text | IoT Platforms and Security: An Analysis of the Leading Industrial/Commercial Solutions

Sensors | Free Full-Text | Influence of Human Factors on Cyber Security within Healthcare Organisations: A Systematic Review

In situ structures of polymerase complex of mammalian reovirus illuminate RdRp activation and transcription regulation | PNAS
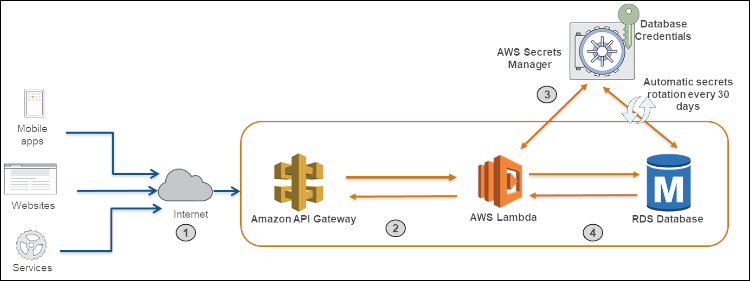
How to securely provide database credentials to Lambda functions by using AWS Secrets Manager | AWS Security Blog